Optimising aircraft turnaround time is a critical task for airlines looking to maximise efficiency and minimise costs. Delays in turnaround time can lead to lost revenue opportunities, as well as increased costs associated with aircraft operations.
Continue readingImproving transported animal welfare for a North American airline
Pets are an integral part of many families, and for pet owners, their furry friends are like family members. When it comes to air travel, it’s essential to ensure that pets are well taken care of and that their safety is a top priority.
Continue readingCargo Dashboard for airlines – An implementation approach
Introduction
- August 9, 2022
To address this complex issue, TCG Digital followed a business-first, design thinking-based approach. The team conducted extensive field studies across 7 hub airports in the US, spending considerable time with ramp personnel and supervisors in the cargo department. They then proceeded with ideation, prototyping, and testing for a month to design a customer experience and lay new business processes. The team prioritized and customized requirements, rapidly built and deployed the final product with the most relevant features, and continually fine-tuned the solution through a feedback-based system.
The result? The Cargo Dashboard, a software product with a plethora of features that revolutionized the cargo department’s operations with the following features:
- Scanner apps to scan cargo items and maintain scan history
- Configurable scan points to let the business decide touch points across which they want cargo tracking
- Real-time monitoring
- Real-time alerts
- Rule-based engine
- Visual tracking
- Use responsive design for unified desktop and mobile experience
- Create, expose or consume micro-service based APIs
- Create real-time alerts in the application for user notifications
Latest Blog
Recent Posts
Managers who are tempted to feel elated at the prospect of having access to all the data they could ever wish for, soon realize it is a data sword of Damocles* hanging by a thread, ready to snap and bury them if they can’t find a way to unlock its value.


* The parable of the sword of Damocles teaches us that no matter how good someone’s life may appear, it’s difficult to be happy living under existential threat.
The architecture followed a loosely coupled approach, reducing single points of failure. Responsive visual design was used, and data was protected during both at rest and on transit by using modern encryption methods, such as HTTPS for data in transit and KMS for data at rest. Best practices of AWS cloud-specific principles were followed, including high availability of the solution with multi-availability zones and caching of resources where possible for a reduced load on computational resources.
Cargo Dashboard Architecture
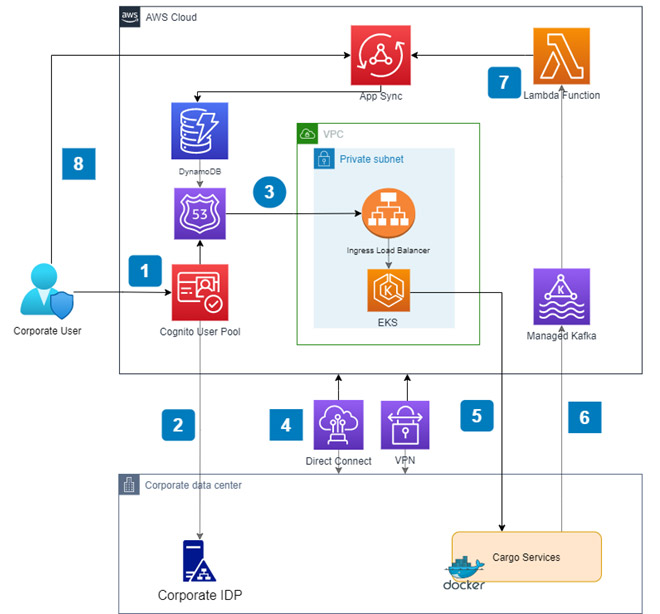
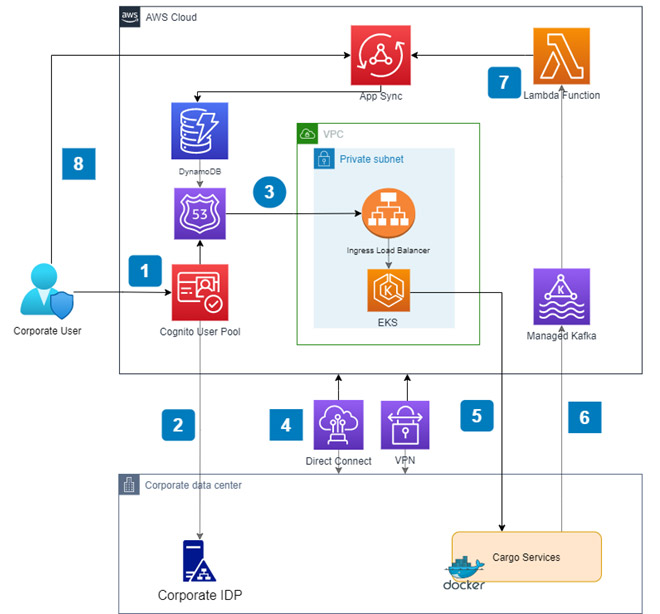
- A corporate user of the dashboard logs in to the application. Cognito User Pool is used to present a login screen to the user where the user enters login credentials.
- Cognito connects with corporate Identity provider to authenticate users. The federation is achieved using a pre- configured trust relationship based on SAML assertions. On successful authentication, Cognito uses a callback Route 53 URL to redirect users to the dashboard landing page.
- Route 53 routes the request to an ingress load balancer deployed within a private subnet. The load balancer sits on top of a set of microservices deployed onto an EKS cluster. The front end is also containerized and deployed on EKS. S3 and Cloudfront were considered as an alternative for the front end. However, Cloudfront was not a whitelisted service at the organization and couldn’t be used.
- To establish a secure connection between AWS cloud and the corporate datacenter Direct Connect is used. An IPsec VPN tunnel is also configured and BGP routing is used to route traffic between cloud and datacenter.
- The microservices connect to corporate cargo services to fetch data for the dashboard. The corporate services essentially act as the backend for the microservices.
- The corporate cargo services generate some alerts to be displayed on the dashboard. These alert messages are pushed to a managed Kafka cluster on the cloud.
- A Lambda function is triggered that reads alert messages from Kafka and mutates those onto an AppSync API. AppSync uses DynamoDB as the backing datastore.
- The dashboard application subscribes to the AppSync API. After each mutation, the dashboard receives the new alert message. If a message is deleted from a dashboard the deletion gets mutated and is reflected in all open dashboards across devices. AppSync also takes care of offline synchronization.
In conclusion, TCG Digital’s business-first, design thinking-based approach enabled them to build a future-proof solution that met the client’s needs. The Cargo dashboard proved to be highly beneficial for the airline as it led to significant improvements in the efficiency and effectiveness of their cargo operations, enabling them to reach new heights.
Cloud Migration & Modernization
Cloud Migration & Modernization
Introduction
- June 7, 2022
However, some organizations are hesitant to begin a cloud adoption journey due to perceived challenges and roadblocks. These first steps are made easier if a cloud migration follows well established strategies. Cloud migration and modernization should be viewed as a continuous process that requires change management spanning people, process and technology. Taking a comprehensive approach will not only help you successfully navigate the journey, but ensure that you realize the intended benefits of being more agile, having the ability to scale, and operational efficiency.
Latest Blog
Recent Posts
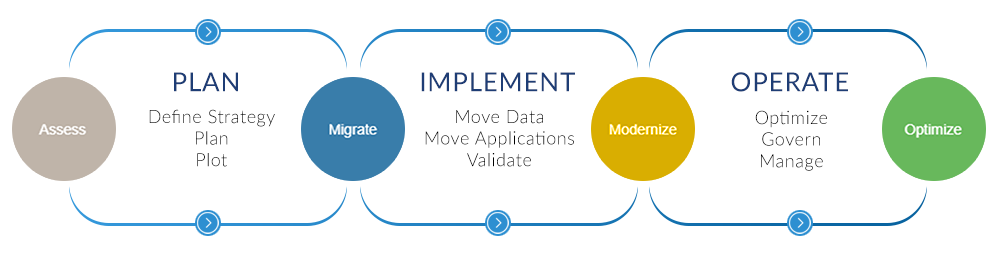
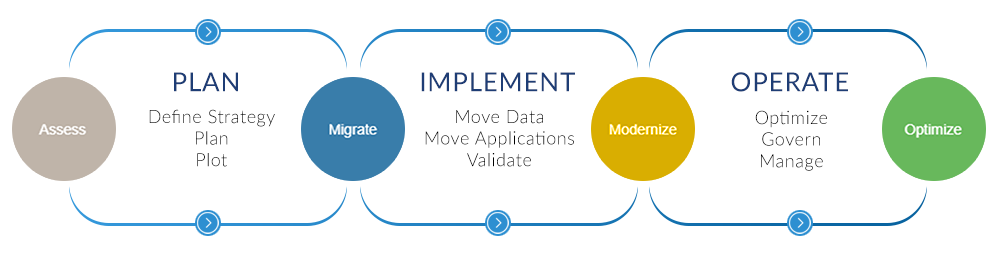


Plan
This phase should start with defining the business benefits and a migration strategy. Defining and documenting business drivers for cloud migration and modernization will clarify the reasons for migrating. The next step is to discover and assess applications, databases and infrastructure. All major cloud platforms provide automated assessment tools that help to get insights on dependencies, create application inventory and assess on-premises environment to get right-sizing guidance, workload level cost estimates and performance metrics.Primary considerations of these assessments include:
- Hardware and performance
- Number of users and licensing issues
- Compliance
- Dependencies between applications
- Easy to migrate
- Difficult to migrate
- Can’t migrate
Implement
Automated migration tools provided by cloud platforms should be used as much as possible to carry out the migration. An iterative process of migrating one workload at a time or a small collection of workloads per release should be looked at. The data should be moved first. This includes moving data to object storage, file systems and databases. The next step is to migrate the applications. This can be a simple “lift and shift” or a re-platforming to the target cloud platform.Once applications are migrated, they should be modernized iteratively. Modernisation involves refactoring, re-architecting or rebuilding your apps and data. Use modernisation to achieve benefits like boosting app innovation, increasing agility and accelerating developer velocity.


Operate
The last phase is to govern and manage the migrated and modernized applications and optimize them continuously in the process. This would include getting visibility into and more control over security in order to quickly detect and respond to threats with intelligent threat detection techniques. Applications should be made redundant across cloud regions and availability zones and a disaster recovery plan should be in place. Also, cloud spending should be adjusted and monitored, thereby driving operational efficiencies.Migrating existing applications to cloud might feel overwhelming with concerns around cost and security. However, if done right, applications on the cloud can be more secure than traditional on-premises deployments. By moving to the cloud, operating costs can be considerably reduced by leveraging a pay-per-use cost model. Also, the use of a proper tools, techniques and frameworks ensure a smooth migration to the cloud and subsequent modernization.
Cargo Landing Page
Accelerate your Aviation Growth through AI-enabled improved Cargo Operations by collaborating with TCG Digital
Why DOWNLOAD
We help you to efficiently resolve all your varied cargo problems. Not just that, we enhance your cargo operations for better performance that significantly leads to improved cargo revenue.
Besides, leveraging our two decades of domain experience, we are leading this journey, with our complete spectrum of digital transformation initiatives encompassing platforms, strategies, technology, and analytics.
Our advanced analytics and AI platform – tcg mcube- helps create the most agile digital ecosystem for all your operations. With a well-defined roadmap, we ensure that you strike the right balance between streamlining your cargo operations and progressive innovation for accelerated growth.
Understand our offerings in detail and make informed decisions on how to deal with an ever-changing cargo landscape.
How Emerging Technologies are reshaping the Future of Retail?
AI is revolutionizing retail
It would not be wrong to state that now is the time for brands to think digital. In their effort to meet changing customer requirements, it is technologies like artificial intelligence (AI) and machine learning (ML) which will help them stay afloat. As compared to traditional analytics, they come with an entirely new level of data processing capabilities which leads to more valuable insights. At present 28% of retailers already deploy AI/ML solutions which equal to a seven-fold increase from 2016 (Source: SPD Group). By adopting AI, retailers can glean valuable insights from customer intelligence and behavioral data and make informed decisions. By capitalizing on AI, specifically on ML retailers are providing immersive experiences to captivate customers, synchronizing offline and online channels for seamless service delivery, and redefining traditional supply chains on the lines of flexible systems which accurately respond to shifting consumer mindsets.Demand forecasting
Amidst all these changes, retailers are faced with one critical question, which is, how will the pandemic impact demand and how can they accurately predict the shift? Many retailers are turning to ML-powered demand forecasting to adapt to today’s reality. In contrast to traditional forecasting methods, this new approach is more adaptable to changes and can be implemented faster. ML enables systems to learn automatically and improve recommendations with data alone, without relying on human intervention for additional programming. As retailers generate large amounts of data, ML technology can often deliver significant business value. When data is fed into an ML system, it searches for patterns and uses them for better decision-making. In most cases, ML makes it possible to incorporate multiple factors and correlations which impact demand into the retail forecasts. And, it is possible to enhance the accuracy of demand forecasting by optimizing the systems with POS data, NLP models, and recent data from external sources.It has been seen that NLP models are often used to analyze social media and news, which in turn helps determine customer sentiment. Text mining and sentiment analysis enable retailers to closely monitor the comments which customers share on social media. This gives them an idea of what customers buy most often, their feedback on the product availability, and their changing preferences. With adequate samples of conversations which customers engage in, NLP models can predict goods which are running out of stock and need to be replenished. They can also detect slight changes in the purchase patterns, thereby improving the accuracy of demand forecasting.
Pricing Optimization
Besides demand forecasting, pricing is another area where ML comes of use. With the dramatic shift to online channels, the pricing strategy and competitive pricing have significant implications for retailers. Those who believe in setting prices based on conventional metrics may fall behind. Machine Learning algorithms can decipher unconventional relationships between multiple parameters which provide valuable insights and help set the optimal price. Specifically, ML helps retailers determine the price elasticity, ie the impact of a price change on a product’s demand. This capability plays a vital role in promotion forecasting and in optimizing markdown prices, especially when retailers need to clear out stocks. However, price elasticity alone might not capture the complete impact of a price change. The prices of alternate products within the same category often have a significant impact as well. Here advanced ML algorithms can be deployed and a product’s price position determined in a straightforward manner.Supply chain management
Apart from forecasting the demand and determining the best price for a product and service, managing the supply chain effectively is equally crucial. Supply chains have always been vulnerable to natural disasters, disruptions and geopolitical issues. But the upheaval caused by the COVID-19 pandemic has been one of a kind. It has led businesses to take a close look at their supply chain management strategies, both for sustainability and growth. It has been seen that predicting the future demand for production remains one critical challenge in supply chain management. Here machine learning takes into account multiple factors which cannot be tracked through existing methods which retailers rely on. ML is used by businesses to conduct an in-depth analysis of individual customers and predict their future buying behavior. This helps tailor the production and transport processes to the actual demand, thereby enabling businesses to deliver value and build a relationship of trust with their customers.On a concluding note
AI and specifically machine learning will impact almost every aspect of retail operating models. While traditional retailers have hesitated to wade into this technology, they cannot wait further. On the other hand, their forward-thinking counterparts who have already embarked on an AI-enabled future are more poised to gain an edge and leapfrog their competition. While there may not be a one-size-fits-all solution, the test-and-learn attitude will help them realize the full potential of emerging technologies.Resources:
- https://www.forbes.com/sites/danielnewman/2020/06/23/4-actionable-customer-experience-statistics-for-2020/?sh=434c4fe91a84
- https://www.salesforce.com/blog/customer-engagement-trends/
- https://us.epsilon.com/pressroom/new-epsilon-research-indicates-80-of-consumers-are-more-likely-to-make-a-purchase-when-brands-offer-personalized-experiences
Recalibrating Customer Experience in the New Normal
Dale Carnegie rightly put it when he said, “When dealing with people, remember you are not dealing with creatures of logic, but creatures of emotion.” These words of the famous American motivational speaker and writer have become even more significant now as businesses try and adapt to changing customer behavior with care and empathy. Within a very brief span of time, COVID-19 has gravely affected the lives and livelihoods of millions across the globe. And, this has led organizations to rethink the definition of customer engagement and service, prompting them to closely monitor customer satisfaction metrics to be able to address their needs accurately.
Understanding customer needs
According to a report by Oracle, 86% of buyers 1 are willing to pay more for a great customer experience. But one daunting question most businesses are faced with is how to approach customer experience (CX) differently in the new normal. Before they can create an engaging customer experience, the first step is to understand what matters most to customers – especially during this disruptive scenario. A Salesforce report suggests that 73% of customers 2 expect organizations to understand their needs and expectations. One of the best ways to gauge their requirements is to intimately understand them – know their persona well. Often, defining the target audience, delving into their demographic profiles and digital footprints can provide insights into their needs and wants.
Role of AI
Businesses are also fast embracing AI technologies such as machine learning to understand the customers accurately. The technologies are being used to gather and analyze historical, social, and behavioral data and gain a better understanding of the customers. AI which continuously improves from the data which it analyzes can accurately anticipate customer behavior. It delivers actionable and real-time customer insights which equip brands to create relevant and thoughtful content across touch points that not only resonate with customers but also improve the chances of sales opportunities and enhance the customer journey.
Need for differentiation
While understanding the customer is important, equally crucial is to differentiate from the competition. If you want to stand out as a brand, you must personalize the customer experience. Close to 80% of customers 3 are more likely to make a purchase when businesses provide personalized experiences. AI helps brands to connect with customers at a more personal level by analyzing customer sentiment and feedback with precision which is not achievable by humans alone. It has also been seen that feedback-driven models foster higher engagement levels, loyalty, and retention.
Why strategize?
However, before looking into AI, what brands need is a CX vision and a robust strategy. While laying down a well-thought-out strategy, brands need to factor in the role of safety and trust. The pandemic has brought forth consumers who are more thoughtful in their decision making and selective when with purchases. They are engaging with brands which demonstrate safety, convenience and trust in experience delivery. Most consumers trust a brand which is good at protecting the privacy of their personal information, delivers quality products and services at fair prices and engages with them in a meaningful way. This is leading forward-thinking brands towards process and business–model innovation at every point of interaction with customers.
Focus on efficiency
Along with this, well-performing brands are prioritizing efficiency. They have realized that to achieve a superior customer experience which is also sustainable; they need to focus on efficiency and convenience. After the onset of the pandemic, customers are no longer willing to understand and tolerate inconvenience despite their loyalty to a trusted company. Companies that opt for the efficiency path to win profitable customers have few factors in common. Most of these companies have access to the data they need and streamline workflows to align with customer journeys. This helps overcome organizational silos and eliminate the habitual repetitive tasks. Moreover, employees working with these brands are empowered to connect the dots between specific customer expectations and interactions. They are prompt in adopting technology to automate routine tasks and deliver consistent experiences across touch-points. Finally, these brands remain focused on supply chain innovation and optimization for seamless service delivery.
Adopting omni-channel strategies
In the wake of the pandemic, there is an increased need for omni-channel strategies. And one among them is to boost customer loyalty through several touch-points. By providing customers with multiple opportunities to connect, brands are driving positive customer experiences and loyalty. As consumer buying habits have changed, with a majority opting for online purchases and ordering in bulk, organizations need to foresee spikes in demand for which they are relying on technology. By investing in technology, they can expect improved inventory management and order routing along with gaining an in-depth knowledge of consumer behavior and preferences.
Omni-channel transformation is the need of the hour where touch-points are not treated in isolation but as part of seamless transitions when customers move from one channel to another. Customer experience journeys cannot be treated as linear but one where there are frequent shifts between traditional and digital channels, which can vary according to customer types and preferences. Understanding the customers’ digital behavior goes a long way in reducing the churn rate. Often the best approach is to promote automated tools and self-service touch-less technology for basic interaction with tech-savvy consumers and appoint highly skilled live agents to handle critical requests.
Final note
From the above discussion we can conclude that the power to differentiate, understand customer needs at a granular level, maintain a focus on efficiency and adopt omni channel strategies are the key factors which can drive an enhanced CX. And this investment in building relationships and delivering a superior experience can help brands to retain valuable customers in the long run. Over and above these, it is critical to understand and prepare for major changes as evolving consumer habits often necessitate a change in the CX strategy not just for sustainability but also for a competitive advantage— the importance of which cannot be overlooked in these uncertain times.
Resources:
- https://www.forbes.com/sites/danielnewman/2020/06/23/4-actionable-customer-experience-statistics-for-2020/?sh=434c4fe91a84
- https://www.salesforce.com/blog/customer-engagement-trends/
- https://us.epsilon.com/pressroom/new-epsilon-research-indicates-80-of-consumers-are-more-likely-to-make-a-purchase-when-brands-offer-personalized-experiences
Digital Transformation in the Post-Pandemic Environment
Change has become imperative with the breakout of the pandemic, which has forced organizations to optimize operation and cost, leading them to rethink their digital transformation strategies. In fact, the pandemic has increased their budgets for digital transformation while breaking down previous inhibitors such as executive approval, legacy software, and the absence of clear strategies. Guided by the broader business strategy, organizations are fast turning to digital technologies to scale up or solve pressing business issues. And the role of technology is not just limited to merely driving marginal efficiency but rather is that of a catalyst which drives innovation and disruption.
On the road to Recovery
It would not be wrong to state that with the onset of the pandemic, digital transformation itself has been disrupted, owing to immediate actions required for crisis and change management. The present nature of the crisis has required teams to act promptly amidst uncertainty and take quick decisions with limited oversight. It has required them to react to fast-changing situations. Here digital transformation can help in a shift to agile decision-making enabling a transformation agenda and helping organizations to move forward despite the challenges posed by the pandemic.
While most organizations have come to terms with the new normal, they want to move forward despite the aftermath. This has led them to brainstorm on new ways to operate in these unusual times. But, at the same time neither do they have a playbook for this nor can they refer to proven case studies. Hence, they have to closely monitor their environment for change and test existing business practices and workflows to identify how digitalization would first help fuel stability, and then growth. They have realized that digitalization is the only way forward which will help address the changing business needs and empower them to make a shift from the “Respond” to the “Recovery” phase during the pandemic. This “Recovery” phase would further determine how well they would thrive in the near future.
The valuable role of AI
In this environment, technology has clearly emerged as a winner. Post COVID-19, consumer behavior will not return to the pre-COVID norms that easily. Online purchases will increase and remote work models are here to stay. As the economies slowly start to reopen, artificial intelligence (AI) will play a needle-moving role in helping companies adapt to the current crisis. As they focus on business continuity plans a majority of companies are likely to deploy AI-enabled solutions to drive topline growth. With its unparalleled potential to discover emerging trends, AI can help hyper-personalize products and solutions, thereby improving customer engagement and sales. It can also contribute to the ideation process of creating new products and accelerate R&D initiatives. As the value creation mechanisms change fast, AI can prove crucial in enabling companies to seize the new opportunities which come their way.
Furthermore, recent findings from Gartner revealed that 74% of companies 1 plan a shift to remote work models post COVID-19. AI-based solutions free up the workforce from repetitive and mundane tasks, allowing them the time to invest in more creative work. During virtual meetings, AI tools increase collaboration and can automatically capture and present additional information such as web links, documents, and videos which not only save time and increase productivity but help employees become more productive. Often, we spend a lot of time scheduling meetings and in finding a suitable time for all attendees. Instead, one can easily use a bot which schedules meetings automatically based on the calendars of invitees, checking for their availability, role and expertise, deciding whether they need to be invited at all.
Tapping into the IoT potential
Besides the trends discussed above, disruptions caused by COVID-19 have reminded us how critical a working supply chain is. According to a recent survey, 75% of organizations in a selected sample experienced supply chain disruptions among which 39% reported severe impacts. This indicates that organizations must adopt a new strategy and here Internet of Things (IoT) could inspire relevant solutions. IoT-based solutions allow for supply chain diversification and real-time monitoring. Through virtualization, they help in creating digital twin models enabling virtual exploration of suppliers and accurate risk assessment.
It has been predicted that with the impact of the pandemic, the IoT market size will grow from USD 150 billion in 2019 to USD 243 billion by 2021 2 , at a CAGR of 13.7%. The critical factors behind this trend also include remote monitoring needs during work from home initiatives, smart payment technologies with minimized human contact, and the increasing demand for wearables.
Rethinking customer experience
Along with rapid transformation to the digital world, leaders also need to focus on successful customer experiences (CX). The way they communicate is becoming increasingly important as most consumers have cut down on spending and are trying products and services mostly out of necessity. Hence, customer experiences need to be frictionless, simple, and personalized. The real focus is on building trust on the foundations of empathy, which makes organizations a trusted advisor in the customer journey. In a recent study, 71% of the respondents 3 agreed that if a brand puts profit over people, they will not be able to trust the brand. Hence, establishing an emotional connection with customers becomes important. Amid this black swan event, both digitalization and CX need to move in tandem for a competitive and cost advantage.
Final thoughts
With the pandemic’s severe impact, companies’ resilience is being tested like never before. As the business landscape shifts towards uncertainty and volatility, organizations have to develop new capabilities and prioritize strategic initiatives where digital transformation will have a critical role to play. As they reimagine business for an ever-changing future—digital technologies, innovation, and CX will remain integral constituents of business continuity plans.
Resources:
- https://www.gartner.com/en/newsroom/press-releases/2020-04-03-gartner-cfo-surey-reveals-74-percent-of-organizations-to-shift-some-employees-to-remote-work-permanently2
- https://www.marketsandmarkets.com/Market-Reports/covid-19-impact-on-iot-market-212332561.html
- https://www.tcs.com/perspectives/articles/revamped-customer-experience-brand-loyalty-post-pandemic
Use of AI and ML in the Fight against the Pandemic
Within a few months of COVID-19, the world has changed and we have been forced to look for solutions everywhere. As we grapple with the pandemic, harnessing the potential of technological advances brings us closer to the belief that we will overcome it. In this endeavor, artificial intelligence (AI) and machine learning (ML) have emerged as two key technologies which empower us to better understand and address the COVID-specific issues. Right from prediction to detection, screening, and diagnosing to inching closer towards a vaccine, these two technologies have a critical role to play.
Using ML to screen patients effectively
With every new pandemic, diagnosing individuals is a significant challenge. As tests are expensive at the beginning conducting them on a large scale is a near-impossible task. Any individual who develops symptoms of COVID-19 would be concerned that they have contracted the disease. Instead of taking medical samples from each patient and waiting for slow reports, a more affordable and faster ML-based test would always prove more useful.
Interestingly, a hospital in Florida was one of the first to use machine learning for a strong response to the virus. As patients enter the hospital an automatic face scan (which is based on ML) is conducted to detect whether they are running a fever. This piece of data plays a critical role in triaging patients. Additionally, ML-enabled bots help patients self-identify the next course of action once they are being detected with mild COVID-like symptoms. This saves doctors from spending excessive time on answering questions of worried patients instead of focusing on the treatment.
Detecting patients at high risk
Once a group of people is tested positive it becomes critical to detect patients at a higher risk of developing serious complications or in need of advanced medical care. While many develop symptoms which are mild others may develop acute respiratory distress syndrome (ARDS) or severe lung disease which needs immediate attention. In this context, significant inroads have been made in research and a forecast model has been proposed which depends on the XGBoost calculation (a machine learning algorithm). It helps detect the seriously sick and predict mortality risk. It takes into account three clinical pointers; lymphocytes, lactic dehydrogenase, and high affectability C-reactive protein, an imbalance in which leads to cell injury, compromised cell immunity, and inflammation, also indicative of pathophysiological progress of COVID-19.
Understanding the spread of the contagion
AI-based predictive modeling does not just help in identifying the infected individuals but also in gauging the severity and spread of the pandemic. Early warning systems which are AI-based mine mainstream news, information in other channels, and online content in multiple languages to detect epidemiological patterns which also complement other healthcare networks and syndromic surveillance. A majority of the countries worldwide have opted for contract tracing systems to ascertain the infection routes by using geo-location data to identify individuals who are coming in close contact with the virus carriers. Immediately, text messages are sent as alerts directing them to self-isolate.
Towards a vaccine
AI has played a critical role in the race to discover a vaccine. By understanding viral protein structures, the technology has suggested probable components of the vaccine. It has also helped medical researchers to scour thousands of literature at an unprecedented pace and arrive at conclusions. As the scientific literature related to COVID continues to grow scientists find it challenging to shortlist papers that are relevant to their specific research. A reputed institute which conducts high-impact research created freely available data sets that are machine readable. This enabled researchers to create and apply NLP algorithms, which would accelerate the process of discovering a vaccine. By connecting the dots between studies, AI makes it possible to identify a hypothesis and subsequently suggests experiments.
Holding on to hope
While modern technologies have helped us so far in this intense battle against the pandemic, we hope that it would continue to assist us in achieving new victories and see to the end of this unfortunate situation. It would not be wrong to assume that the possibility of combining ML, AI, and other convergence points of sectors such as healthcare and life sciences presents a brilliant opportunity for new drug discovery. And, as we leverage this opportunity, we will only stand to gain.
Transitioning Back to Work—Strategies You cannot ignore
In the last few months, the COVID-19 crisis has caused unprecedented disruptions in the workplace. This has led organizations to make difficult decisions as they balance between the needs of the business and that of the employees. Along with it, the lockdown restrictions are gradually phasing out and most are preparing to reopen the workplaces. However, to limit the exposure and transmission of the disease, adherence to regulations is critical. It has become imperative for companies to review their existing policies and think of new policies which limit exposure and transmission of the disease.
A center of command
As organizations reflect over new workforce strategies, this will not be a typical recovery. Given the lack of available therapy and the uncertainty over the vaccine, organizations will have to plan for multiple time horizons and scenarios. They may even have to plan for multiple waves of the pandemic considering the resurgence of the virus in countries which had declared themselves virus-free. When we think of alternative ways of working, the critical question which comes up is do we need a command center? Do critical leaders need to be a part of this core group which will help in restarting operations? Will they be able to help in managing external stakeholders? Will the command center be connected to necessary sources for updated news and information which directly affect the business?
Turning to analytics
The next important decision is whether to use analytics and dashboards for informed decision making. What data do organizations need to make accurate quantitative decisions and how do they ensure that they continue to get updated information even from sources beyond the command center? These are questions which companies need to delve into. Data and technology can be used to visualize scenarios and predict what may come next. This scenario planning through analytics will provide business leaders an accurate view of how their decisions will affect customers, staff, and the operational capacity. It may make a significant difference in a strong continuity plan.
A return to work plan has two important components—workplace management and leadership intervention, which we discuss further.
Office and site management
For a successful transition to work, the first step is to decide on the number of employees returning to the office. Higher the number of employees returning to the workplace, the greater is the risk. This requires a staggered reintroduction and smart workforce scheduling. Determining functions, work, and roles that need to return to workplace and those that can continue to work remotely can help in creating effective rosters and prevent the spread of the disease. For teams working remotely, organizations need to provide adequate support and training.
While reopening workplaces, businesses will need to observe the regulations around social distancing and hygiene practices. Reconfiguring office spaces may prove critical as the requirement for six feet impacts seating arrangements. Organizations may have to set up barriers between workstations and also provide personal protective equipment such as gloves, masks, and eye wear. Additionally, they cannot overlook the basic prevention measures such as routine environmental cleaning and disinfection.
Effective leadership for workforce management
As organizations embark on their process of recovery, they have to commit to the physical, psychological, and financial well-being of their employees. Physical well-being will include a stronger emphasis on safety, easy access to testing, and social distancing. Psychological well-being can be ensured through practices such as flexible schedules and adequate support from managers. It is critical to recognize the diversity of the workforce and help them transition to recovery. The commitment to well-being may have to be extended to the employees’ well-being at home, where they continue to take care of their children or the elderly.
While people priorities remain on top of mind for leaders they need to factor in employee morale. While a percentage of the workforce continues with remote work it brings its own set of challenges. Often they have to juggle priorities and the boundaries increasingly become unclear between work and personal time. The responsibility lies with the team leader to strengthen the team now and help them build mental resilience. During these times of uncertainty, it is up to them to provide support and demonstrate compassion.
Hence it’s a holistic approach which can help organizations tide over these difficult times. It would not be wrong to assume that COVID-19 has reinforced our conviction that human concerns cannot be overlooked, especially for organizations looking to resume operations and adapt to new ways of working. In fact, this crisis provides organizations with a valuable opportunity to build a strong connection with employees and pave the way for a resilient response to the pandemic. Do you agree?
[email-download download_id=”9583″ contact_form_id=”7713″]
[email-download download_id=”9446″ contact_form_id=”7713″]
Error: Contact form not found.
Watch the mcube video
The retailer client wanted a data-driven scientific approach to unlock business potential. This platform would take into account multiple predefined business dimensions to enable its reporting and business KPI dashboard and unlock answers for critical business questions via deployment of analytics solutions on a single platform tcg mcube. With Artificial Intelligence and Machine Learning capabilities built in the platform, this project would lay the foundation of a powerful data science journey and create differentiated value.The retailer client wanted a data-driven scientific approach to unlock business potential. This platform would take into account multiple predefined business dimensions to enable its reporting and business KPI dashboard and unlock answers for critical business questions via deployment of analytics solutions on a single platform tcg mcube. With Artificial Intelligence and Machine Learning capabilities built in the platform, this project would lay the foundation of a powerful data science journey and create differentiated value.